Auto logout in seconds.
Continue LogoutThis week, Quest Diagnostics and Laboratory Corp. of America released securities filings disclosing that data on 11.9 million Quest customers and 7.7 million LabCorp patients might have been affected when an "unauthorized user" gained access to American Medical Collection Agency's (AMCA) system.
Check out our new cybersecurity cheat sheet series
Quest says 11.9M patients' data might have been affected by breach
Quest Diagnostics on Monday disclosed that an "unauthorized user" had access to American Medical Collection Agency's (AMCA) system and might have accessed data on 11.9 million Quest patients.
Quest in a statement said AMCA on May 14 alerted Quest and Optum360, one of Quest's contractors that uses AMCA's billing collection services, that an unauthorized user had access to AMCA's systems between Aug. 1, 2018, and March 30, 2019. According to Quest's securities filing, the data stored by AMCA included financial information—such as credit card numbers and bank account information—medical information, and other personal information, such as Social Security Numbers. The data did not include lab results.
Quest said AMCA has not provided "detailed or complete information about the AMCA data security incident, including which information of which individuals may have been affected." However, Quest said it is working to verify the information AMCA has provided.
Quest also said it has stopped sending collections to AMCA and is complying with all notification regulations. "We are committed to keeping our patients, health care providers, and all relevant parties informed as we learn more," Quest said.
Quest added that it will work with AMCA, Optum360, and third-party security experts to conduct an investigation of the breach. Quest said patients with questions about the breach can contact the company's customer service hotline at 866-MY-QUEST.
AMCA said it has "hired a third-party external forensics firm to investigate any potential security breach in [its] systems, migrated [its] web payments portal services to a third-party vendor, and retained additional experts to advise on, and implement, steps to increase [its] systems' security."
A spokesperson for UnitedHealth Group, Optum360's parent company, said Optum360's systems were not affected by the security incident. UnitedHealth Group said it is working with Quest and AMCA to make sure appropriate steps are taken to address the breach.
The Daily Briefing is published by Advisory Board, a division of Optum, which is a wholly owned subsidiary of UnitedHealth Group.
LabCorp says 7.7M patients' data might have been affected by breach
LabCorp in its securities filing said the addresses, balance information, dates of birth, dates of service, health care providers, names, and phone numbers of about 7.7 million of its patients also might have been exposed in the breach. "AMCA's affected system also included credit card or bank account information that was provided by the consumer to AMCA (for those who sought to pay their balance)," the filing stated.
LabCorp, which is one of the world's leading commercial laboratory testing companies, said it does not send AMCA any diagnostic information or laboratory results, so such information was not at risk. LabCorp also noted that AMCA does not store insurance identification information or social security numbers for LabCorp patients.
LabCorp said it has stopped sending collection requests to AMCA and has suspended the collection firm's work on pending requests that involved LabCorp patients.
LabCorp's securities filing stated that AMCA is sending notices to about 200,000 consumers whose bank account or credit card information might have been exposed in the breach, and offering affected consumers credit monitoring services and identity protections services for two years (Thomas, Wall Street Journal, 6/4; Tyko, USA Today, 6/4; NBC 4 New York, 6/4; Uchill, Axios, 6/3; Truong, MedCity News, 6/3; Chin, Wall Street Journal, 6/3; Rowland, Washington Post, 6/3).
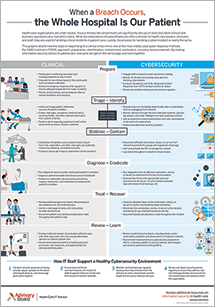
Next, check out our new cybersecurity cheat sheet series
Executives need to play a crucial role in cybersecurity strategy. While the chief information officer (CIO) and chief information security officer (CISO) will be critical partners, they can't be left to lead the charge all on their own. For example:
- The board can ensure mechanisms in place to track security status and progress;
- The CEO can include cybersecurity in due diligence of any M&A or partnership activity;
- The CMO and CNO can make the clinical voice heard in the organization's security governance;
- The CFO can ensure funding requests for security tools and services are vetted against a security strategy and roadmap;
- The COO can ensure business continuity plans are in place, tested, and work well across all shifts; and
- The CHRO can ensure the security team has the necessary staff to operationalize its security strategy.
Want to learn more about what you should be doing in your role? Check out our cybersecurity cheat sheet series which outline what executives in every role should be doing—and the key questions they should be asking—to help their organizations stay secure.
Don't miss out on the latest Advisory Board insights
Create your free account to access 1 resource, including the latest research and webinars.
Want access without creating an account?
You have 1 free members-only resource remaining this month.
1 free members-only resources remaining
1 free members-only resources remaining
You've reached your limit of free insights
Become a member to access all of Advisory Board's resources, events, and experts
Never miss out on the latest innovative health care content tailored to you.
Benefits include:
You've reached your limit of free insights
Become a member to access all of Advisory Board's resources, events, and experts
Never miss out on the latest innovative health care content tailored to you.
Benefits include:
This content is available through your Curated Research partnership with Advisory Board. Click on ‘view this resource’ to read the full piece
Email ask@advisory.com to learn more
Click on ‘Become a Member’ to learn about the benefits of a Full-Access partnership with Advisory Board
Never miss out on the latest innovative health care content tailored to you.
Benefits Include:
This is for members only. Learn more.
Click on ‘Become a Member’ to learn about the benefits of a Full-Access partnership with Advisory Board
Never miss out on the latest innovative health care content tailored to you.